1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
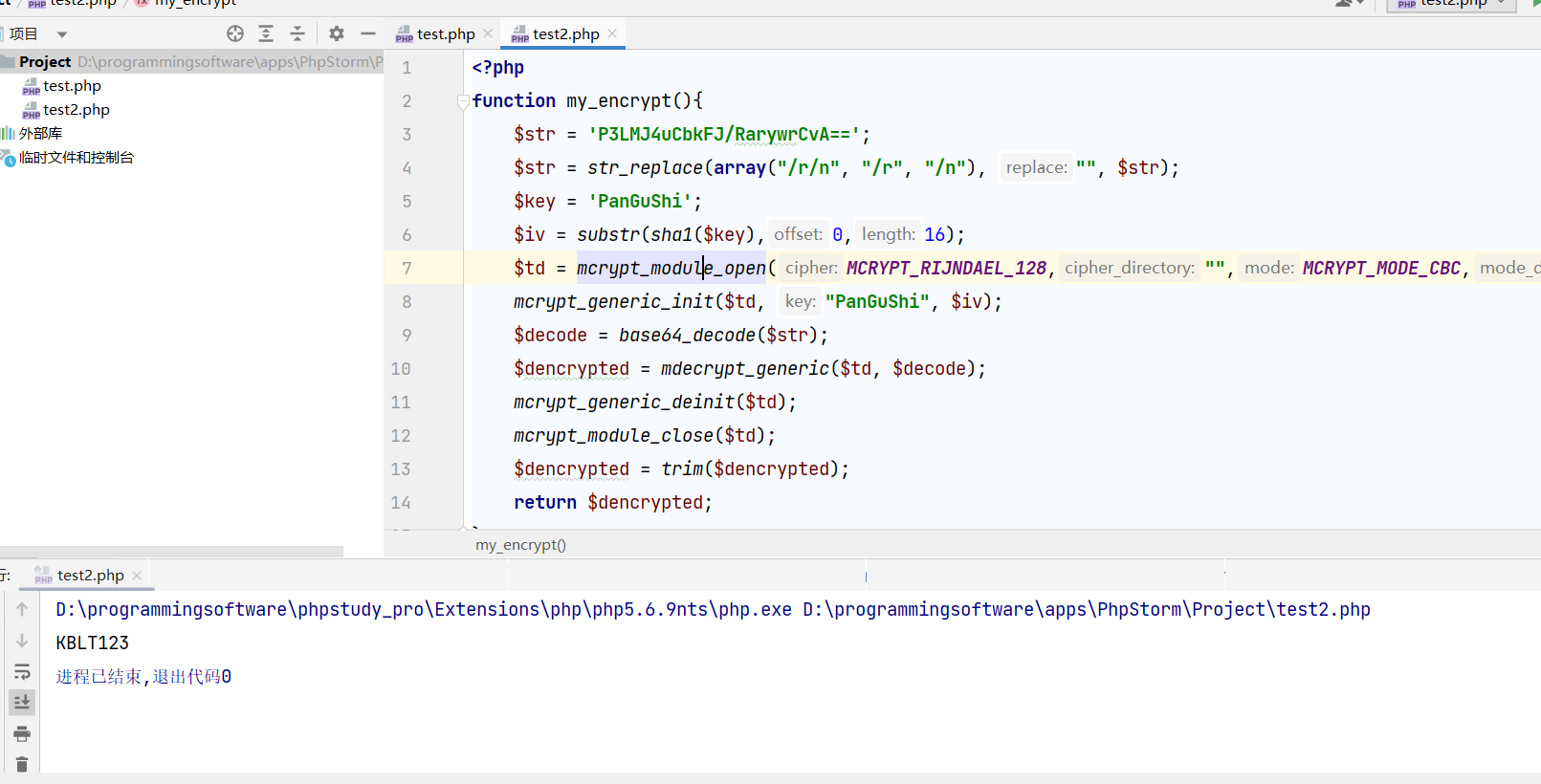
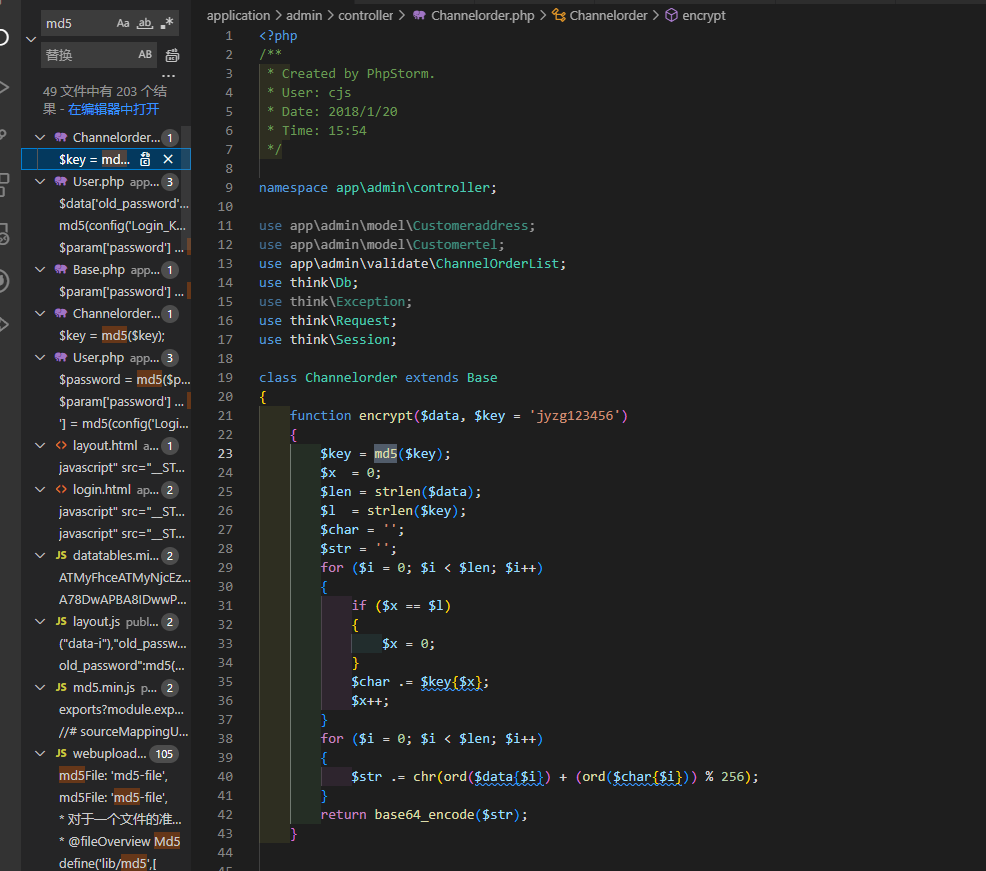
| from hashlib import md5
from itsdangerous import base64_decode
import requests
b=[('2', 'RMB', 0.04, 2),
('3', 'RMB', 0.06, 3),
('4', 'RMB', 0.05, 4),
('5', 'RMB', 0.07, 5),
('6', 'RMB', 0.10, 6),
('7', 'RMB', 0.15, 7),
('8', 'RMB', 0.17, 8),
('9', 'RMB', 0.23, 9),
('10', 'RMB', 0.22, 10),
('11', 'RMB', 0.25, 11),
('12', 'RMB', 0.29, 12),
('13', 'RMB', 0.20, 13),
('14', 'RMB', 0.28, 14),
('15', 'RMB', 0.33, 15),
('16', 'RMB', 0.35, 16),
('17', 'RMB', 0.35, 17),
('18', 'RMB', 0.37, 18),]
a=[(142, '943617668819', 'GG币', 2, 5, 3, 'mZVymm9t'),
(144, '588047503620', 'GG币', 2, 5, 3, 'lpxqlXFo'),
(150, '597613045539', 'GG币', 2, 5, 3, 'l5xummto'),
(167, '368360644631', 'GG币', 2, 5, 3, 'm5Zwm3Bn'),
(187, '704008760599', 'GG币', 2, 5, 3, 'nJhtlGlm'),
(189, '695829830065', 'GG币', 2, 5, 3, 'm5tpmGtm'),
(197, '689591506416', 'GG币', 2, 5, 3, 'm5ptnGtu'),
(199, '296524099918', 'GG币', 2, 5, 3, 'mZlym25r'),
(209, '202884729901', 'GG币', 2, 5, 3, 'm5hpnHBu'),
(210, '955226714946', 'GG币', 2, 5, 3, 'm5prlm9u'),
(227, '421623628935', 'GG币', 2, 5, 3, 'nJlyl2hu'),
(245, '228102248133', 'GG币', 2, 5, 3, 'lptummhs'),
(263, '279069782487', 'GG币', 2, 5, 3, 'lpxrl21n'),
(317, '911539892864', 'GG币', 3, 5, 3, 'mZRpnHBs'),
(358, '940690024660', 'GG币', 3, 5, 3, 'mZpxm2lr'),
(371, '703759626723', 'GG币', 3, 5, 3, 'm5dtmGls'),
(405, '250826052511', 'GG币', 3, 5, 3, 'mpxvlnBv'),
(418, '699369204729', 'GG币', 3, 5, 3, 'mJpynHBt'),
(441, '110783516494', 'GG币', 3, 5, 3, 'nJZwm2lu'),
(448, '754012259548', 'GG币', 3, 5, 3, 'mpdtnWxq'),
(452, '999734985528', 'GG币', 3, 5, 3, 'nJdtlmpr'),
(457, '259291480194', 'GG币', 3, 5, 3, 'mZtymHBm'),
(468, '672136643928', 'GG币', 3, 5, 3, 'nJlslmpp'),
(486, '995091488940', 'GG币', 4, 5, 3, 'l5RunW1p'),
(493, '369911062367', 'GG币', 4, 5, 3, 'nJxplXFm'),
(494, '627743356329', 'GG币', 4, 5, 3, 'lZdpmm1s'),
(496, '341907225040', 'GG币', 4, 5, 3, 'mZZwnW9u'),
(541, '505274522158', 'GG币', 4, 5, 3, 'mJVrmmhp'),
(558, '465727738353', 'GG币', 4, 5, 3, 'lZZwl3Bs'),
(575, '801973338928', 'GG币', 4, 5, 3, 'm5xvm2hm'),
(588, '990446771976', 'GG币', 4, 5, 3, 'mpZslmpm'),
(595, '443752577679', 'GG币', 4, 5, 3, 'mZtrnGtp'),
(598, '274195438646', 'GG币', 4, 5, 3, 'lp1rm21t'),
(605, '389442476686', 'GG币', 4, 5, 3, 'nJxplmtp'),
(651, '840764463035', 'GG币', 5, 5, 3, 'l5twlXFq'),
(667, '575571956339', 'GG币', 5, 5, 3, 'lphqmm9s'),
(693, '369199269150', 'GG币', 5, 5, 3, 'm51wmG1q'),
(706, '299510640482', 'GG币', 5, 5, 3, 'mJlxlWto'),
(731, '660695028585', 'GG币', 5, 5, 3, 'lJ1vmXFq'),
(738, '856482910335', 'GG币', 5, 5, 3, 'mpVpmW5r'),
(756, '750042176098', 'GG币', 5, 5, 3, 'm5lrlGpr'),
(784, '651691106346', 'GG币', 5, 5, 3, 'mpxplm9u'),
(786, '255787712926', 'GG币', 5, 5, 3, 'lZpxnHFn'),
(791, '135691319557', 'GG币', 6, 5, 3, 'nJdymWpm'),
(819, '788431214978', 'GG币', 6, 5, 3, 'mJpum3Fo'),
(850, '851409238798', 'GG币', 6, 5, 3, 'lpRrmWto'),
(873, '260951952586', 'GG币', 6, 5, 3, 'lZtunXBv'),
(885, '231265027253', 'GG币', 6, 5, 3, 'lpprnWtt'),
(930, '262701249039', 'GG币', 6, 5, 3, 'lJdslnBr'),
(977, '184134048308', 'GG币', 7, 5, 3, 'lJZrnWpm'),
(979, '391202213852', 'GG币', 7, 5, 3, 'l5Zrm21m'),
(1004, '325182412061', 'GG币', 7, 5, 3, 'lJdul2hm'),
(1009, '145997703051', 'GG币', 7, 5, 3, 'mphylG9q'),
(1029, '812286624781', 'GG币', 7, 5, 3, 'lZhpm2pp'),
(1051, '932860292032', 'GG币', 7, 5, 3, 'lZ1qnW1s'),
(1074, '960800718320', 'GG币', 7, 5, 3, 'nJ1tlHFp'),
(1079, '309703180719', 'GG币', 7, 5, 3, 'mZxqm2tp'),
(1080, '867260227199', 'GG币', 7, 5, 3, 'mZdsm21t'),
(1088, '489129121639', 'GG币', 7, 5, 3, 'mpRvlG9o'),
(1094, '640176750934', 'GG币', 7, 5, 3, 'mJVqlmhv'),
(1097, '271657786070', 'GG币', 7, 5, 3, 'mJRwlHBq'),
(1119, '895632760061', 'GG币', 8, 5, 3, 'l5dtmWtt'),
(1164, '291179495316', 'GG币', 8, 5, 3, 'mZdylHFt'),
(1170, '588053366224', 'GG币', 8, 5, 3, 'l5RqlWxn'),
(1171, '308892834659', 'GG币', 8, 5, 3, 'mZ1um3Fs'),
(1181, '712419993689', 'GG币', 8, 5, 3, 'lJ1rnWhu'),
(1185, '240497645432', 'GG币', 8, 5, 3, 'm5pulWhv'),
(1193, '519564426335', 'GG币', 8, 5, 3, 'lptrnW1u'),
(1218, '178274213935', 'GG币', 8, 5, 3, 'm5xynWxn'),
(1243, '621845480580', 'GG币', 8, 5, 3, 'lpRynGtr'),
(1246, '984927062919', 'GG币', 8, 5, 3, 'mpxulGlm'),
(1255, '508590678286', 'GG币', 8, 5, 3, 'nJdslm9r'),
(1261, '165679472688', 'GG币', 8, 5, 3, 'lJhslHBq'),
(1272, '398566701812', 'GG币', 8, 5, 3, 'nJpwnWhu'),
(1299, '391669188513', 'GG币', 9, 5, 3, 'mptql2tv'),
(1328, '308977433705', 'GG币', 9, 5, 3, 'l51xmmlp'),
(1347, '128173141307', 'GG币', 9, 5, 3, 'mZVymXFn'),
(1375, '315017222711', 'GG币', 9, 5, 3, 'lJhqnW5q'),
(1390, '698730100843', 'GG币', 9, 5, 3, 'm5ppmGpr'),
(1394, '454661923665', 'GG币', 9, 5, 3, 'mZlqm21t'),
(1446, '770844458971', 'GG币', 9, 5, 3, 'mpZslWxt'),
(1461, '336049994728', 'GG币', 10, 5, 3, 'mJ1pnHFm'),
(1503, '900217499326', 'GG币', 10, 5, 3, 'l5drlXBp'),
(1515, '541334504409', 'GG币', 10, 5, 3, 'mJlvmW1u'),
(1520, '296235199037', 'GG币', 10, 5, 3, 'mZtxlG5t'),
(1522, '961454505603', 'GG币', 10, 5, 3, 'nJtsnHFn'),
(1540, '660586887840', 'GG币', 10, 5, 3, 'l5Rvm29o'),
(1542, '521373859771', 'GG币', 10, 5, 3, 'm5xvlWxv'),
(1558, '690490467926', 'GG币', 10, 5, 3, 'm5Zrl2xm'),
(1615, '915839175755', 'GG币', 11, 5, 3, 'mZlwlG1u'),
(1667, '731272590033', 'GG币', 11, 5, 3, 'nJpvlWtr'),
(1676, '266051494236', 'GG币', 11, 5, 3, 'mJxym25s'),
(1677, '952748053664', 'GG币', 11, 5, 3, 'lpVqnWxv'),
(1721, '432188794976', 'GG币', 11, 5, 3, 'mZVvl3Fq'),
(1730, '923396563975', 'GG币', 11, 5, 3, 'lZVtlW5m'),
(1731, '188214551206', 'GG币', 11, 5, 3, 'lZRqlGhn'),
(1737, '562343715793', 'GG币', 11, 5, 3, 'nJxqm2hn'),
(1788, '723775062575', 'GG币', 11, 5, 3, 'nJVtl21s'),
(1814, '437640662866', 'GG币', 12, 5, 3, 'lJdumWlq'),
(1847, '261181748262', 'GG币', 12, 5, 3, 'mJtxmGtp'),
(1866, '520680592708', 'GG币', 12, 5, 3, 'mZxsnHFv'),
(1893, '846224640296', 'GG币', 12, 5, 3, 'lpdtl2xn'),
(1901, '526823225486', 'GG币', 12, 5, 3, 'mphqlm5p'),
(1919, '293881600039', 'GG币', 12, 5, 3, 'lJdxlGpn'),
(1986, '252943398463', 'GG币', 13, 5, 3, 'lpVvlHFu'),
(2050, '841971039165', 'GG币', 13, 5, 3, 'lJhvmHBn'),
(2051, '113568559627', 'GG币', 13, 5, 3, 'l5xunGtv'),
(2059, '884517377766', 'GG币', 13, 5, 3, 'lZRul2pt'),
(2065, '429478659168', 'GG币', 13, 5, 3, 'mpdqnGxu'),
(2081, '701817809209', 'GG币', 13, 5, 3, 'l5Zxlmho'),
(2093, '648527268061', 'GG币', 13, 5, 3, 'lJppmWhq'),
(2118, '346397347560', 'GG币', 13, 5, 3, 'nJVylWpp'),
(2121, '598070757264', 'GG币', 13, 5, 3, 'm5VxnWlr'),
(2144, '385475471817', 'GG币', 14, 5, 3, 'lpdsnGtq'),
(2152, '860407002245', 'GG币', 14, 5, 3, 'mZ1tnGpt'),
(2175, '876730476520', 'GG币', 14, 5, 3, 'mJVqmmtq'),
(2226, '705271590445', 'GG币', 14, 5, 3, 'l5hslWhm'),
(2260, '778005846695', 'GG币', 14, 5, 3, 'lZZtl21r'),
(2265, '429472355879', 'GG币', 14, 5, 3, 'nJlumGlm'),
(2279, '837352974915', 'GG币', 14, 5, 3, 'lJhsmW9t'),
(2304, '206040245526', 'GG币', 15, 5, 3, 'lZZym25s'),
(2347, '214154454225', 'GG币', 15, 5, 3, 'l5tpnHBt'),
(2353, '539433927736', 'GG币', 15, 5, 3, 'nJVunG1q'),
(2371, '614328206854', 'GG币', 15, 5, 3, 'mJdtlHFu'),
(2373, '744073817220', 'GG币', 15, 5, 3, 'mpVtlnFp'),
(2386, '472576318606', 'GG币', 15, 5, 3, 'mplrnG1t'),
(2393, '905356397967', 'GG币', 15, 5, 3, 'mJ1ylHBr'),
(2408, '202047690664', 'GG币', 15, 5, 3, 'nJhynG5m'),
(2419, '660557237414', 'GG币', 15, 5, 3, 'mplymG1r'),
(2518, '284536429033', 'GG币', 16, 5, 3, 'lJtxlGxo'),
(2537, '846259865921', 'GG币', 16, 5, 3, 'lpRxnGlm'),
(2539, '914271862202', 'GG币', 16, 5, 3, 'mZxwnG5s'),
(2569, '230868458507', 'GG币', 16, 5, 3, 'mZptnWpn'),
(2592, '580327294210', 'GG币', 16, 5, 3, 'mJZylGxq'),
(2601, '113725129935', 'GG币', 16, 5, 3, 'mZZvm3Fo'),
(2614, '125295831828', 'GG币', 17, 5, 3, 'lJdxnW9t'),
(2622, '304246628524', 'GG币', 17, 5, 3, 'lZtxmXFv'),
(2636, '949878301272', 'GG币', 17, 5, 3, 'nJxtlXFm'),
(2642, '236806705755', 'GG币', 17, 5, 3, 'mJZumW1r'),
(2644, '219250916132', 'GG币', 17, 5, 3, 'nJ1tmG1p'),
(2653, '856797267940', 'GG币', 17, 5, 3, 'mplslmpu'),
(2709, '829562956572', 'GG币', 17, 5, 3, 'lJZxlG5p'),
(2751, '904086289177', 'GG币', 17, 5, 3, 'nJtxmXBq'),
(2796, '568416612736', 'GG币', 18, 5, 3, 'lZdxmmtq'),
(2817, '987519535765', 'GG币', 18, 5, 3, 'lJdrlG1o'),
(2880, '657461012245', 'GG币', 18, 5, 3, 'mpZtmmlm'),
(2906, '278546157230', 'GG币', 18, 5, 3, 'mJVxnGpm'),
(2921, '999235838187', 'GG币', 18, 5, 3, 'mJVwmWxu'),
(2935, '861319935688', 'GG币', 18, 5, 3, 'mplslWps'),]
sum=0
def fun(sttr,key=b'jyzg123456'):
return float(requests.get("http://192.168.0.222/test.php?str="+sttr).text.strip())
for i in a:
sum+=b[i[3]-2][2]*fun(i[6])
print(sum)
|